Installing the Security Configuration Wizard
After
you have installed Windows Server 2003 SP1 or higher, you are ready to
install SCW. To install the wizard, do the following:
1. | In Control Panel, double-click Add or Remove Programs.
|
2. | Click Add/Remove Windows Components, and then select the Security Configuration Wizard check box.
|
3. | Click Next to install the utility.
|
Running SCW
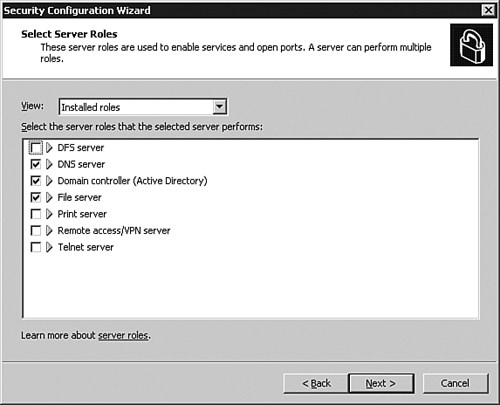
The
SCW is installed in the Administrative Tools section of the Start menu.
When you run the SCW, you will have an opportunity to select what roles
the server plays. Note that the SCW has already selected the roles that
it is aware of, as shown in Figure 3.
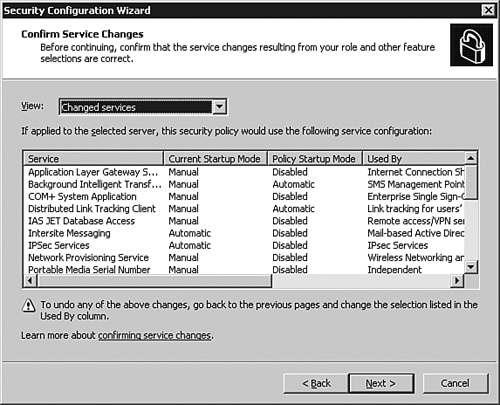
The
SCW continues, giving you the opportunity to select client features
(such as domain name system [DNS], Dynamic Host Configuration Protocol
[DHCP], or the Automatic Update Client), and installed options (such as
a global catalog, Windows Firewall, or time synchronization). Finally,
there might be an additional screen for additional services. After you
have selected all of the appropriate features, you must confirm service
changes. A sample of the changed services can be seen in Figure 4.
The
SCW continues through network security changes (locking down unused
ports), Registry settings, and configuring policy auditing. After
finishing, you have the option to apply the security policy to the
computer immediately, or save it to apply to this server (or other
servers) later.
Securing Servers with Security Templates
Security
templates are a practical and effective means to apply security
policies and configurations to Exchange servers. Although security
templates are provided with Windows
Server 2003, it is recommended to customize them prior to applying them
using the Security Configuration and Analysis Microsoft Management
Console (MMC) snap-in.
This not only
ensures that computers are identically configured with the same
security configurations, but it also is an easy way to configure
appropriate security measures for those computers that are not managed
using GPOs.
Note
Microsoft
creates Exchange-specific security templates and distributes them
through their website. However, at the time of this writing, the
security templates for Exchange Server 2007 have not yet been released.
Keeping Up with Security Patches and Updates
One
of the least glamorous, but most important, security measures an
organization can take is to ensure all of their products have the
latest security patches implemented in a timely fashion. Applying
service packs, security updates, and hotfixes for the operating system,
as well as applications such as Exchange 2007, are crucial to
maintaining a secure environment. As security shortcomings are
identified, these service packs and hotfixes close the holes, often
before they become publicly known, effectively protecting your
environment from malicious users.
Note
Thoroughly
test and evaluate service packs and hotfixes in a lab environment
before installing them on production servers. Also, install the
appropriate service packs and hotfixes on each production server to
keep all systems consistent.
Windows Update
Windows
Update is a web service, accessed in Microsoft Internet Explorer
(Tools, Windows Update) that scans a local system and determines if the
system has all current updates installed. This tool is extremely useful
on individual systems, but can be time consuming when used to update
multiple systems within an organization.
Windows Server Update Services
Windows
Server Update Services (WSUS), an upgrade from its predecessor Software
Update Services (SUS), minimizes administration, management, and
maintenance of small- to midsized organizations by allowing them to
communicate directly and securely with Microsoft to gather the latest
security updates and service packs. WSUS is available for Windows
Server 2003 and for Exchange servers.
The primary differences between WSUS and its predecessor are as follows:
Support for a greater number of products, including service pack updates
The ability to target computers using Group Policy or scripts
Reports on update installation status
Performs basic hardware inventory
With
WSUS, the updates are downloaded from Microsoft to a local WSUS server.
They can then be distributed to a lab environment for testing, or to
targeted production servers. After being tested and approved, WSUS can
be used to automatically distribute the updates thoughout your
environment. By utilizing this service, updates can be downloaded from
Microsoft once, and distributed locally, saving a significant amount of
bandwidth when compared to hundreds (or thousands) of systems each
downloading the updates themselves.