Keeping Services to a Minimum
Depending
on the role that an Exchange Server 2007 server will fulfill, not all
services that are installed by default are necessary for the server to
function. It is considered a best practice to limit the number of entry
points (services) into a server to only those required. Any services
that are not necessary for the system to operate properly should be
disabled. Although this can be done manually on a server-by-server
basis, it can also be performed using a customized security template to
ensure all servers in your environment are configured properly.
Locking Down the File System
Files
stored on a Windows Server 2003, including mail databases, are only as
secure as the permissions that are assigned to protect them. As such,
it is good to know that Windows Server 2003 (for the first time in a
Microsoft operating system) does not grant the Everyone
group full control over share-level and NTFS-level permissions by
default. In addition, critical operating system files and directories
are secured to disallow their unauthorized use.
Despite
the overall improvements made, a complete understanding of file-level
security is recommended to ensure that your files are properly
protected.
Note
For
increased file-level security, the Exchange Server 2007 installation
process requires that partitions on the underlying operating system are
formatted as NTFS.
Using the Microsoft Baseline Security Analyzer
The
Microsoft Baseline Security Analyzer (MBSA) is a tool that identifies
common security misconfigurations and missing hotfixes. This
information is gathered via local or remote scans of Windows systems.
MBSA allows administrators to have the ability to scan a single Windows
system and obtain a security assessment, as well as a list of
recommended corrective actions. In addition, administrators can use the
MBSA tool to scan multiple functional roles of a Windows-based server
on the network for vulnerabilities. This allows administrators to
ensure systems are up to date with the latest security-related patches.
Figure 2 shows a sample output from the MBSA.
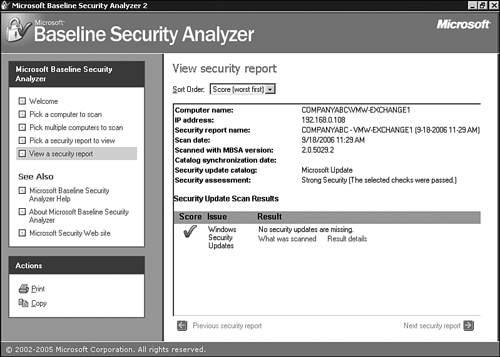
The MBSA can be downloaded from the Microsoft website at http://www.microsoft.com/mbsa.
Implementing Industry Standards and Guidelines
As
discussed previously, Microsoft has gone to great lengths to provide
secure and reliable products. Moreover, it has worked closely with
companies, government agencies, security consultants, and others to
address security issues in the computer industry.
In
addition to Microsoft security standards and guidelines, it is
advisable that organizations use recommended best practices compiled by
the National Institute of Standards and Technologies (NIST) and the
National Security Agency (NSA). Both NIST and NSA provide security
lockdown configuration standards and guidelines that can be downloaded
from their websites (http://www.nist.gov and http://www.nsa.gov, respectively).
Using the Security Configuration Wizard
The
Security Configuration Wizard (SCW) is an attack-surface reduction tool
for the Windows Server 2003 with Service Pack 1 or later. The SCW
guides administrators in creating security policies based on the
minimum functionality required for a server’s role or roles.
SCW reviews the computer configuration, including but not limited to, the following:
Services— SCW limits the number of services in use.
Packet filtering— SCW can configure certain ports and protocols.
Auditing— Auditing can be configured based on the computer’s role and the organization’s security requirements.
Internet Information Services (IIS)— SCW can secure IIS, including web extensions and legacy virtual directories.
Server roles and tasks—
The role (file, database, messaging, web server, and so on), specific
tasks (backup, content indexing, and so on), and placement in an
environment of a computer is a critical component in any lockdown
process or procedure. Application services are
also evaluated from products such as Exchange Server, SQL Server, ISA
Server, SharePoint Portal Server, and Operations Manager.
Caution
The
SCW is a very flexible and powerful security analysis and configuration
tool. As a result, it is important to keep control over when and how
the tool is used because system performance can be greatly degraded
while the wizard is running. Equally important is testing possible
configurations in a segmented lab environment prior to implementation.
Without proper testing, environment functionality can be stricken or
completely locked.
The
SCW is used to assist in building specific security-related policies
and to analyze computers against those policies to ensure compliance.
SCW actually combines many of the security-related tasks performed by
several other Microsoft security tools. For instance, SCW can take
existing security templates created from the Security Configuration and
Analysis tool and expand upon the restrictions to meet an
organization’s security policy requirements. In addition, SCW can
analyze computers for any security updates that are needed, integrate
with Group Policy, and provide a knowledge base repository