The previous section presented in great level of
detail the theory of operations of a flexible and scalable access
control architecture that leverages some characteristics of the TACACS+
protocol design and the maturity of Cisco Secure ACS product.
The concepts previously discussed for IOS are still
valid for ASA, but some configuration and implementation details are
different. The examples analyzed in this section point out the relevant
distinctions.
Example 1 reminds you that individual command authorization is not supported by RADIUS.
Example 1. Individual Command Authorization Is Not Supported by RADIUS
! Verifying the available arguments for the command "aaa authorization command"
ASA1(config)# aaa authorization command ?
configure mode commands/options:
LOCAL Predefined server tag for AAA protocol 'local'
WORD Specify the name of a TACACS+ aaa-server group to be used for command authorization
|
Example 2
shows the baseline configuration for enabling command authorization and
accounting on ASA.
Example 2. Basic Configuration for ASA Command Authorization and Accounting
! Defining an AAA server-group called TACACS1
aaa-server TACACS1 protocol tacacs+
aaa-server TACACS1 (dmz) host 172.21.21.250
key cisco123
!
! Defining the LOGIN authentication method for the console line
aaa authentication serial console LOCAL
!
! Defining TACACS+ as the method for Telnet Authentication
aaa authentication telnet console TACACS1
!
! Defining TACACS+ as the method for Enable Authentication
aaa authentication enable console TACACS1
!
! Defining EXEC session authorization (does not include console line)
aaa authorization exec authentication-server
!
! Accounting, for all the configured forms of access, uses TACACS+
aaa accounting telnet console TACACS1
aaa accounting serial console TACACS1
!
! Defining TACACS+ as the method for command authorization
aaa authorization command TACACS1
!
! Defining TACACS+ as the method for command accounting
aaa accounting command TACACS1
|
Note
In IOS, you can assign a value of “15” to the user
privilege level (priv-lvl=15) during EXEC authorization. This approach
makes it possible for IOS to eliminate the enable authentication
process and rely on shell command authorization sets for authorizing
commands of any level. ASA does not enable the priv-lvl to be directly
assigned and does requires the aaa authentication enable console command .
Example 3
depicts a command authorization failure for ASA. Authorization failures
do not generate accounting records because accounting, strictly
speaking, is associated with successful operations (authentication or
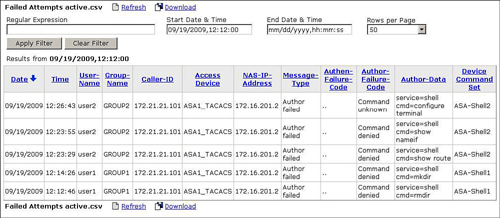
authorization). Refer to Figure 1, which shows a sample log of Failed Attepts of command execution in CS-ACS (Reports and Activity session).
Example 3. User Issues Command not allowed by Shell Command Set
! Command "show route" not authorized
mk_pkt - type: 0x2, session_id: 417
mkpkt - authorize user: user2
cmd=show
cmd-arg=route Tacacs packet sent
Sending TACACS Authorization message. Session id: 417, seq no:1
Received TACACS packet. Session id:1761304772 seq no:2
tacp_procpkt_author: FAIL
TACACS Session finished. Session id: 417, seq no: 1
|
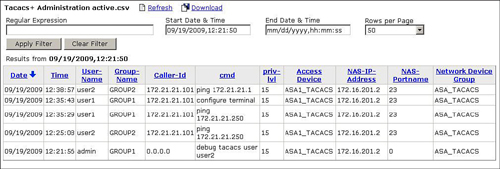
Examples 4 and 5 contrast ASA behavior about command accounting when a show command is issued. Although the show command is individually authorized, ASA does not send an accounting message registering it.
Figure 2 displays some examples of command accounting for the ASA. Notice the absence of show commands in the CS-ACS report.
Example 4. User Issues an Authorized “show” Command
|
! Command "show uauth" is authorized. No accounting happens for "show commands"
mk_pkt - type: 0x2, session_id: 421
mkpkt - authorize user: user2
cmd=show
cmd-arg=uauth Tacacs packet sent
Sending TACACS Authorization message. Session id: 421, seq no:1
Received TACACS packet. Session id:1409549404 seq no:2
tacp_procpkt_author: PASS_ADD
tacp_procpkt_author: PASS_REPL
TACACS Session finished. Session id: 421, seq no: 1
|
Example 5. User Issues Authorized Command (not a “show” command)
! User issues "ping 172.21.21.1" (successful authorization and accounting)
mk_pkt - type: 0x2, session_id: 419
mkpkt - authorize user: user2
cmd=ping
cmd-arg=172.21.21.1 Tacacs packet sent
Sending TACACS Authorization message. Session id: 419, seq no:1
Received TACACS packet. Session id:998474355 seq no:2
tacp_procpkt_author: PASS_ADD
tacp_procpkt_author: PASS_REPL
TACACS Session finished. Session id: 419, seq no: 1
!
mk_pkt - type: 0x3, session_id: 420
mkpkt - accounting username: user2
remote ip : 172.21.21.101 task_id=40
Tacacs packet sent
Sending TACACS Accounting message. Session id: 420, seq no:1
Received TACACS packet. Session id:15914798 seq no:2
TACACS Session finished. Session id: 420, seq no: 1