Most UK websites will fall foul of an EU
directive on the use of cookies when it comes into force on 26 May, according
to a report by KPMG - despite having a year’s notice.
The consultancy firm surveyed the sites of
55 major UK organizations and found 96% didn’t comply with the requirements.
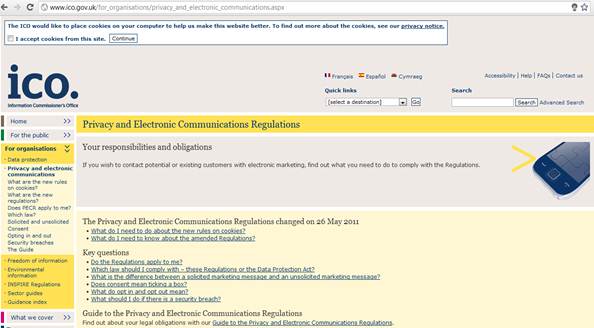
The ICO, responsible for enforcing the new rules, asks cookies on
its own site (top). But how many users want browsing to be interrupted by these
requests?
The EU directive on Privacy and Electronic
Communications was implemented in a change to the Privacy and Electronic
Communications Regulations that came into force on 26 May 2011. But the UK
Government said it would take time for site owners to put the necessary
‘technical measures’ in place, and the Information Commissioner’s Office, which
enforces the regulations, announced a 12-month ‘lead-in’ period. It stressed,
though, that ‘organisation should be taking steps to ensure they can properly
comply with the revised rules for cookies by May 2012’, after which those found
to be in breach could be fined up to $775675.
The directive requires that before websites
place cookies (small data files) on a user’s computer that pass information to
third parties, they must first obtain explicit consent from the user. Of the
websites surveyed by KPMG, only one of the 53 that used cookies asked users to
opt in. Stephen Bonner, of KPMG’s Information Protection and Business
Resilience team, said: ‘While the majority of the websites we analyses made a
reference to the use of cookies... and some also state how the cookies are
being used, this is not enough to ensure compliance.’
Bonner advised organisation to conduct an
inventory of their websites and the cookies they use, evaluate their purpose
and put together a plan, which should include adding consent requests to
cookies related to logging in, registration and similar processes. Organisation
should have a schedule for adding consent for other cookies, and should take
legal advice on their obligations.

The
EU directive on Privacy and Electronic Communications was implemented in a
change to the Privacy and Electronic Communications Regulations that came into
force on 26 May 2011.
Such use of cookies is widespread, and many
in the industry doubt if the legislation is helpful. Copywriter Rachel
McCombie, posting at SE Optimize, was ‘quite angry’ at ‘a pointless bit of
bureaucracy that is disruptive to both users and webmasters’. But Jim Killock
of the Open Rights Group pointed out that the purpose of cookies ‘has been
extended to profile your movements around commercial sites purely to help
advertisers’.
Although the directive will be enforced
across the EU from 26 May, the Information Commissioner, Christopher Graham,
said last year there would be no “wave of formal enforcement actions against
those who are not yet compliant but are trying to get there.’ The key, then, is
to be seen to be trying.
“I’m quite angry at a pointless bit of
bureaucracy that is disruptive to users and webmasters’”