Trojan Horses At The Gates Of
OSX
New backdoor vulnerability proves to be an advanced persistent threat
for Mac users
It is quite
rare to hear of attacks on the OSX ecosystem, but the few times it has
happened, it raised a significant number of alarms culminating in an 'end of
days'-like responses.
New Mac OS X Backdoor Trojan
Discovered
It has
happened again recently as a new Trojan called the Flashfake Trojan has spread
on Macs, creating a botnet consisting of over 700,000 computers. Kaspersky
Lab's researchers have discovered another malicious program that targets Macs,
which has been confirmed as an Advanced Persistent Threat. Unlike
the Flashfake Trojan, the new, more malicious Backdoor.OSX. SabPub.a is
a real threat for users as attackers can gain full control of their computers.
Kaspersky
Lab's experts set up a fake victim machine, infected by the backdoor, and on 15
April discovered some unusual activity. The attackers seized control of the
infected system and started analysing it. They sent commands to view the
contents of root and home folders and even downloaded some of the fake
documents stored in the system.
This
analysis was most likely performed manually, and not using some automated
system, which is unlikely in the widespread "mass-market" malware.
Therefore, it can be confirmed that this backdoor is an example of an Advanced
Persistent Threat in active use.
Alexander
Gostev, Chief Security Expert at Kaspersky Lab, commented: "The SabPub
backdoor once again reveals that not a single software environment is
invulnerable. The relatively low number of malware for Mac OS X does not mean
better protection. The most recent incidents like Flashfake and SabPub indicate
that the personal data of unprotected Mac users is also at risk, either because
cybercriminals understand the rising market share of such machines, or because
they are hired for the direct task of attacking Apple computers."
Android Fortified
Avira
launches free Android security software
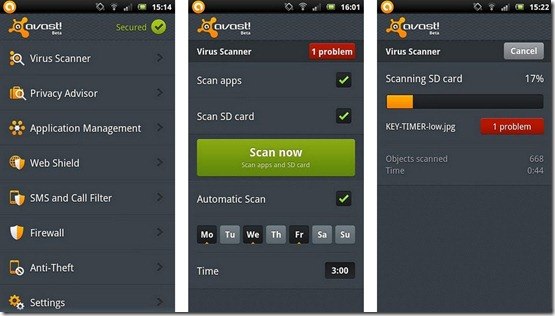
Cases of smartphone theft has been constantly on the rise. To that end,
Avira has seen fit to launch its own Avira Free Android Security software that
helps users remotely locate, lock or erase an Android phone from everywhere in
the world.
"Since
malware threats for Android are still relatively uncommon, we first focused on
anti-theft and remote device management features in Avira Free Android
Security," said Jerome Chan, general manager of Avira SEA.
Avira Free
Android Security comes with Avira Android Web Console, which lets you manage up
to five phones remotely. The Web Console also lets you handle behind-the-scenes
chores like activating/ deactivating phones, remotely checking phone activity,
current battery level, device model number and device IMEI number.
Avira Free
Android Security is compatible with Android versions 2.2 (Froyo) and 2.3
(Gingerbread) and is available now for download in English.
Picture Imperfect
Fake
Instagram for Android app loaded with malware

Ever since
Instagram made it to the Android Play Store, the response towards the photo
taking and sharing app has been tremendous. Recently bought over by Facebook,
the app has been downloaded approximately about 5 million times in less than a
week of it being launched for the Google mobile operating system.
Sophos, an
IT security team is reminding Android users to only download the app via a
trusted source such as the Play Store. There have been reports going around of
a fake Instagram APK file that is circulating around the Internet, and if
installed, will send background SMSes to premium rate services, earning money
for the cybercriminals.
"Just
last week, we saw a bogus edition of the Angry Birds Space game and it's quite
likely that whoever is behind this latest malware are also using the names and
images of other popular smartphone apps as bait." said Graham Cluley,
senior technology consultant at Sophos.
LulzSec Beheaded
Leader
of hacking group turns in own members
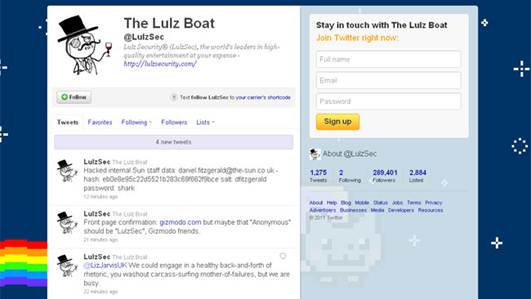
LulzSec claimed responsibility for the attack
on their Twitter acount
LulzSec, a
hacking group that is an offshoot of Anonymous, has seen several of its top
members getting caught from law enforcement agencies in a crackdown that spans
a few continents.
Some
sources said the crackdown happened mostly due LulzSec's leader, identified as
Hector Xavier Monsegur, nicknamed Sabu, an unemployed 28 year old father of two
was caught last year. It is said that ever since the FBI made his identity
public, he became a cooperating witness.
"They
caught him and he was secretly arrested and now works for the FBI," a
source close to Sabu told FoxNews.com.
As a result
of Monsegur's cooperation, the remaining top-ranking members of LulzSec were
arrested or hit with additional charges. The five charged in the LulzSec
conspiracy indictment were identified by sources as: Ryan Ackroyd and Jake
Davis, both of London; Darren Martyn and Donncha O'Cearrbhail, both of Ireland;
and Jeremy Hammond of Chicago.
Data Theft Of The Month
Gamigo
hacked!
Gamigo, a
free-to-play MMO games library service has recently seen its website hacked,
as users have run into problems trying to access the service. Gamigo's staff
detected an illegal intrusion into its user database and has resulted in a
temporary closure in account registration, account management and payment
services. Despite this however, Gamigo has reiterated that the gaming
services have not been affected by the attack, and the game servers are still
secure.
Nasa
admits stolen laptop contains iss codes
NASA has
recently admitted that a laptop that was stolen back in 2011 had contained
codes to control the International Space Station. The unencrypted laptop went
missing last year and resulted in the loss of algorithms to control the ISS.
Despite this however, NASA has said that at no point in time that the ISS was
in jeopardy due to the data breach. Martin said software vulnerabilities in
NASA machines often go unpatched and only 1 percent of NASA mobile devices
are encrypted. He said that until the space agency can implement an
agency-wide encryption policy, data stored on mobile devices will remain at
high risk.
Hacked,
again!
Not too
long after being hacked by a 17 year old from Morocco, which saw information
on 350,000 customers being spread out in the open, DigitalPlayground has been
hacked yet again, with 73,000 email addresses, usernames and passwords. It is
said that 40,000 credit card numbers containing CCV code and expiration dates
were also obtained from the attack. At the time of writing,
Digitalplayground.com is accessible. But the site does not allow the
registration of new users.
|