The
Windows Server 2008 R2 server role that handles NAP is the Network
Policy Server role. Installing this role on a server effectively makes
it an SHV and an Enforcement Server. The specific role added to the
Server Role Wizard is called the Network Policy and Access Services
role, and includes the following components:
Routing and Remote Access Service (RRAS)—
The server role that provides for virtual private network (VPN)
capabilities, allowing for clients to “tunnel” their communications in
an encrypted fashion across an insecure network such as the Internet.
The role services included with this role include the Remote Access
Service, which provides VPN support, and the Routing service, which
provides software-based routing capabilities on the server itself.
Host Credential Authorization Protocol (HCAP)—
An industry-standard protocol that is used when integrating Microsoft
NAP with the Cisco Network Access Control Server. This allows the
Windows NPS role to examine Cisco 802.1X access client health.
Health Registration Authority (HRA)—
A server that distributes health certificates to clients that pass
health policy checks. The HRA is only used in Microsoft’s NAP
implementation for IPSec enforcement.
Network Policy Server—
The Windows Server 2008 R2 role that acts as a NAP Health Policy Server
and a Remote Authentication Dial-In User Service (RADIUS) server for
authentication and authorization.
Exploring NPS Concepts
The Network Policy
Server role in Windows Server 2008 R2 allows for the creation of
enforcement policies that apply to the following types of network
access:
Internet Protocol Security (IPSec)—
IPSec encryption allows for all communications, even those that would
normally be unencrypted, to be highly secured through PKI-based
encryption. IPSec can be configured to be required between servers, and a
system configured with the NPS role can regulate which clients are
allowed as IPSec clients based on their local health.
802.1X authentication—
802.1X is a network-based authentication method that uses PKI-based
certificates to authenticate that the user who attaches to the network
is who he claims to be. 802.1X authentication is often used on wireless
fidelity (Wi-Fi) networks. A system with the NPS role in Windows Server
2008 R2 can add clients to the 802.1X network based on their health
status.
Virtual private network (VPN) connections—
A VPN connection allows for traffic to be sent in an encrypted tunnel
across an untrusted network such as the Internet. VPNs are often used by
roaming users to connect to the internal local area network (LAN) of an organization. The NPS role includes support for restricting client VPN access based on system health.
Dynamic Host Configuration Protocol (DHCP) addresses—
One very useful NPS enforcement method is the ability to restrict which
clients get DHCP addresses based on their system health. Although this
is the easiest NAP policy to set up, this is also the easiest to
circumvent as clients could set their own IP addresses.
Understanding RADIUS Support on a Network Policy Server
As previously mentioned,
installing the Network Policy and Access Services role adds support for
the RADIUS protocol, an industry-standard authentication mechanism
supported by a wide range of clients.
Note
The NPS role in Windows
Server 2008 R2 is the replacement for the legacy Internet Authentication
Service (IAS) role. The old IAS role provided simple RADIUS
authentication support to Active Directory sources.
RADIUS authentication
allows for Active Directory users to be authenticated using RADIUS
authentication, rather than AD DS authentication. This is commonly used
in scenarios where VPN access requires RADIUS authentication, or when
other devices cannot use AD-based authentication.
RADIUS client support is
limited to a maximum of 50 clients and two remote RADIUS server groups
with the Standard Edition of Windows Server 2008 R2. Enterprise and
Datacenter Editions offer unlimited support. Windows Web Server 2008 R2
does not support NPS.
Installing a Network Policy Server
Installation of the
Network Policy and Access Services role installs the Network Policy
Server component and the RADIUS role. To install, perform the following
steps:
1. | Open Server Manager (Start, All Programs, Administrative Tools, Server Manager).
|
2. | Click the Add Roles link in the Actions pane.
|
3. | On the Welcome page, click Next to continue.
|
4. | From the list of roles to install, select Network Policy and Access Services from the list, and click Next to continue.
|
5. | Review the information provided on the Welcome page, and click Next to continue.
|
6. | On the Select Role Services page, shown in Figure 1,
select which role services to install on the server. Click Next
to continue.
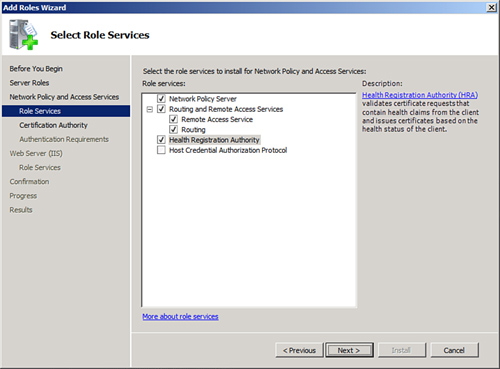
Note
Adding the Health
Registration Authority role service requires the IIS Web Server Role to
be installed on the server. Selecting the role service might prompt you
to install these services as well.
|
7. | On
the Certificate Authority page, choose whether to install a local CA
for issuing health certificates or to use an existing remote CA. If
using a remote CA, make sure it is dedicated to issuing only health
certificates. In this example, we install a local CA; this will install
AD Certificate Services (AD CS) on the system. Click Next to continue.
|
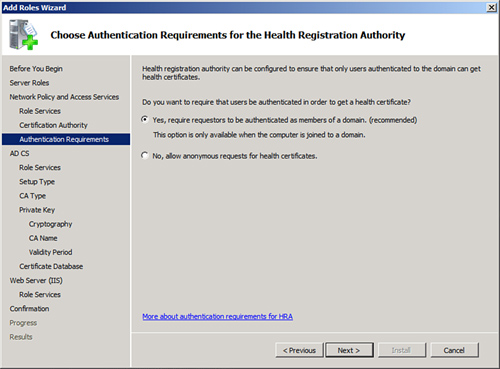
8. | Select whether to configure the HRA to allow only domain-authenticated users to get health certificates, as shown in Figure 2.
This can improve security, but might not be wanted in environments with
untrusted domains or with workgroup members. Click Next to continue.
|
9. | If
installing AD CS on the server, the wizard will lead you through the AD
CS installation process.
|
10. | If
installing the IIS role on the server, the wizard will lead you through
the IIS installation process.
|
11. | On the Confirmation page, click Install.
|
12. | Click Close when the wizard completes.
|