Enamored by Wi-Fi’s convenience, we tend to be blind
to its risks. Many routers are riddled with security holes that leave your data
exposed to enterprising hackers and other intruders. And if you run a business,
the jeopardy is even greater. To keep your wireless network secure, follow
these eight security tips.
1.
Change the default password
If you didn't do it when you set up your router,
immediately change its default password. The default passwords for all vendors
of network equipment are widely known and just a quick search away. (For more
on wireless network setup, see go.pcworld.com/ wifi setup.)
2.
Use only WPA2 encryption
The unidirectional nature of Wi-Fi signals necessitates the
use of encryption to prevent neighbors or malicious parties from spying on your
online activities. Even though the option is still available for legacy
reasons, avoid WEP encryption, as it can be cracked in minutes.
Use only WPA2, which introduces a new AES-based encryption
for better security over WPA. There's really no excuse not to: Today every
Wi-Fi router bearing the Wi-Fi trademark supports it, as does every wireless
device and Wi-Fi adapter card made in the past few years.

Use a complex
passphrase
3.
Use a complex passphrase
Despite the lack of known weaknesses in WPA2, it remains
susceptible to brute-force attacks when used with an easily guessed passphrase.
Specialized software makes it trivial for attackers to process captured
wireless data packets against huge dictionary lists to obtain a match. To foil
such attacks, use a passphrase containing at least 25 characters including a
mix of letters (upper-and lowercase), numerals, and symbols.
4.
Avoid common SSID names
One common tip is to not broadcast the SSID (Service Set Identification)
of your wireless network. While it could be used to throw off novice attempts
at breaking in, hiding the SSID is useless against a half-competent hacker.
But it's good practice to not use the default SSID, or any
common names (go.pcworld.com/ ssid names). Hackers have developed pre-computed
tables of password hashes known as "rainbow tables" to find the WPA
passphrase quickly. Because these tables are keyed to individual SSIDs, using
an SSID that is not on such a table or list would force an attacker to adopt a
more time-consuming approach without the benefit of a ready-to-use rainbow
table.
Avoid common SSID
names
5.
Disable WPS
If your Wi-Fi router supports Wi-Fi Protected Setup (WPS),
disable it. Created as a user-friendly way for users to add new devices to
their network, the WPS PIN is an 8-digit number printed on the label of
WPS-enabled devices. Depending on vendor implementation, however, this is
likely to be susceptible to brute-force attacks.
An attacker can crack the PIN code of a vulnerable device in
between four to ten hours (go.pcworld.com/reaver) of automated effort, which
would allow the attacker to recover your secret pass phrase and make changes to
your Wi-Fi hardware.

WPS makes it
easier to add a device to your network, but it also makes your network more
vulnerable.
6.
Set up a guest network
It would be bad form to deny friends and relatives access to
your Wi-Fi network when they're visiting. But circulating the static passphrase
to everyone is bad security. Instead, set up a separate wireless network under
a second SSID, a feature supported by an increasing number of wireless routers.
Having a separate network for guests allows you to routinely change the
passphrase without affecting your own devices. You can even disable it entirely
when not in use.
7.
Forget MAC address filtering
The MAC (media access control) address is a unique
identifier hardcoded to individual Ethernet ports and Wi-Fi devices. However,
its actual effectiveness is dubious, since it's trivial to spoof a MAC address.
Unless you know what you're doing, we would advise against
MAC address filtering, given the inconvenience and hassle that can result from
a misconfiguration. And having to manually add every single tablet or
smartphone that you acquire is a productivity downer.
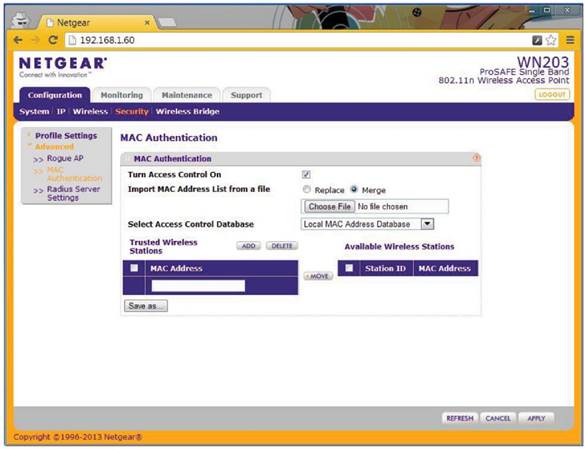
An access point
may let you filter out unauthorized MAC addresses, but see tip 7.
8.
Disallow admin access from the wireless network
You may not be able to keep a determined hacker out, but you
don't have to make his job easier. Disallowing administrative access from the
wireless network should keep any successful hacker from wreaking further havoc
by making changes to the configuration of your Wi-Fi router. Obviously, this
means that any tweaks to your Wi-Fi router would have to be done from a desktop
or laptop on your wired local area network. But the added protection is worth
the hassle.
The tips here aren't meant to exhaustively coverall possible
security risks of a Wi-Fi network, but adhering to these eight tips should make
you significantly safer. Ultimately, though, if security is paramount, sticking
to a wired Ethernet network may be your best bet.