Migration tables are used to
translate security principals and UNC paths from one domain to another.
Because these objects and paths differ in different domains (either in
the same forest or a different forest), the values must be updated when a
GPO is migrated from the source domain to the target domain.
Migration tables can be updated manually,
automatically, or by using the Migration Table Editor. The manual method
is not suggested, because the migration table is stored in XML format
and syntax is extremely important; one minor mistake could make the
migration fail. Migration tables are saved with a .migtable extension
and can be located anywhere on the system that you desire. However,
users who want to use a migration table must have the appropriate
permissions to the file during the migration process.
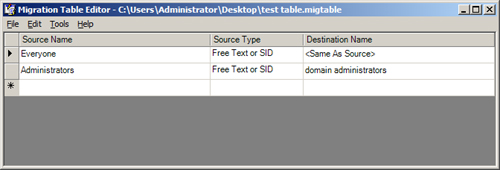
A migration table itself is simple, containing only three variables: source name, source type, and destination name. Figure 3 illustrates what a typical migration table looks like in the Migration Table Editor through the GPMC.
Source name
The source name is the name of the security principal or UNC path in
the source GPO. If the source name does not match the entry in the
source GPO, the migration might fail. The syntax for the source name is
important; Table 1 provides examples of what each source name would look like for the different source types.
Table 1. Source Name Syntax
| Object Type | Example Syntax |
|---|
| User | UPN: [email protected]
SAM: FABRIKAM\Bruno
DNS: Fabrikam.com\Bruno |
| Domain Global Group | UPN: Domain [email protected]
SAM: FABRIKAM\Domain Admins
DNS: Fabrikam.com\Domain Admins |
| Domain Local Group | UPN: [email protected]
SAM: FABRIKAM\Administrators
DNS: Fabrikam.com\Administrators |
| Universal Group | UPN: Enterprise [email protected]
SAM: FABRIKAM\Enterprise Admins
DNS: Fabrikam.com\Enterprise Admins |
| Computer | UPN: [email protected]
SAM: FABRIKAM\Client1
DNS: Fabrikam.com\Client1 |
| UNC Path | \\Server1\Data |
| Free Text or SID | “PilarA”
“S-1-5-21-1473733259-1489586486-3363071491-1005” |
Note
SIDs cannot be referenced in the destination name field. |
Source type
The source type depicts the type of entry that is in the table. This is
either a security principal or UNC path. There are many source types
that can be configured. The following are all of the source types that
can be included in a migration table:
User
Computer
Domain Local Group
Domain Global Group
Universal Group
UNC Path
Free Text or SID
Destination name
The destination name refers to the name that is used in the target
domain for the source name translation. For example, there might be a
group in the source domain named HRAdmins, whereas in the target domain
it is named HRAdministrators. The source name would be HRAdmins and the
destination name would be HRAdministrators. You have a few options in
the destination name field, other than the explicit name of the
destination object. Table 2 lists a few of the other entries and their meanings.
Table 2. Destination Name Entries
| Destination Name Entry | Description |
|---|
| Same as source | This will not modify the security principal or UNC path during the migration. |
| None | This will remove the entry from the source GPO when it is migrated to the target GPO (cannot be used with UNC path). |
| Map by relative name | This will be a translation based on name, such as DomainA\user1 to DomainB\user1 (cannot be used with UNC path). |
| Explicitly specify value | This is where a name is typed into the destination name, providing the exact literal value. |
To create a migration table, it is best to use
the Migration Table Editor, which allows you to work with the migration
entries directly. The most efficient solution is to populate the
migration table directly from the GPO in production or a GPO that has
been backed up. To populate the migration table from a GPO that is in
production, follow these steps:
1. | In the GPMC, right-click the Group Policy Objects node, and then click Open Migration Table Editor.
|
2. | In the Migration Table Editor, click Tools, and then click Populate From GPO.
|
3. | Select the domain in which the GPO resides from the Look In This Domain list.
|
4. | Select the GPO from the Group Policy Objects list.
Note If
you want to include the security permissions that are configured on the
GPO itself, you must also select the check box labeled During Scan,
Include Security Principals From The DACL On The GPO. |
|
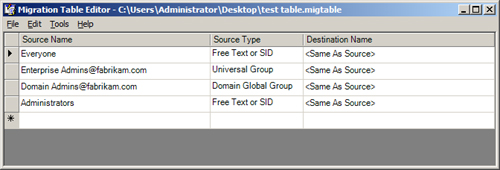
5. | Click OK, and review the results from the scan in the Migration Table Editor, as shown in Figure 4.
|
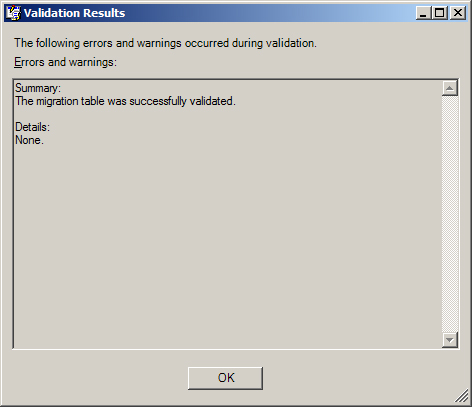
You can save a migration table and validate its
entries. You save the table like any other file—click File, and then
click Save. To validate the file and entries, click Tools, and then
click Validate Table. The Validation Results dialog box indicates
whether there are any issues with the table, as shown in Figure 5.